Open Defense Initiative
We're offering up to $5 million in depthfirst credits for critical open source projects to discover, validate, and remediate vulnerabilities before they can be exploited.
.png)

“Open source maintainers are often the last line of defense for infrastructure that millions of people depend on. Having a partner like depthfirst focused on this problem is exactly what the community needs right now.”
The Open Defense Initiative highlights our commitment towards the mission of securing the world’s software.
We’re offering up to $5 million in depthfirst credits for critical open source projects to use depthfirst to find and fix real, exploitable vulnerabilities. This defensive technology needs to be available to maintainers of all critical open source projects, not just a select few organizations.
depthfirst is on a mission to secure the world’s software, and this requires building the best defensive AI technology and giving all defenders access to it before they are attacked. That mission has never been more urgent. Mythos and GPT-5.5 Cyber have shown a leap in autonomous vulnerability discovery and exploitation. While access to these frontier models is still limited today, open source models are quickly catching up, and bad actors will soon have access to that technology without any filters or guardrails. We now have a short window of time to equip defenders before that happens.
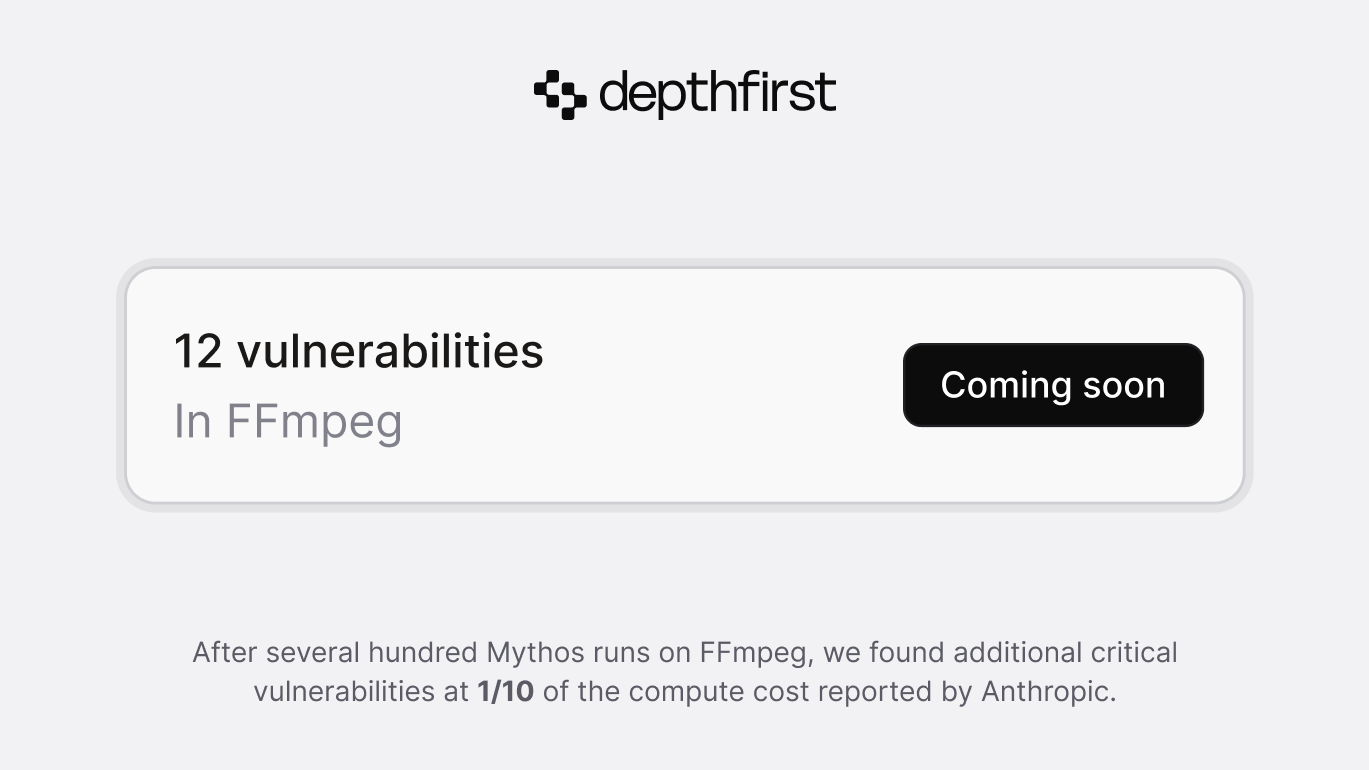
We have built a mission-driven and world class engineering, AI research, and security research team to build a state of the art model, harness, and platform. We can achieve results comparable to the most advanced models like Mythos or GPT-5.5-cyber, but at a fraction of the compute cost. Our platform autonomously found and generated fixes for 12 memory corruption vulnerabilities in FFmpeg that remained after Anthropic ran several hundred scans with its most advanced model, Mythos. We spent $1,000 in depthfirst compute costs to detect them, compared to the $10,000 reported by Anthropic.
This reinforces a core thesis behind depthfirst: in security, model strength alone is not enough. We’re grateful to frontier AI labs for developing stronger general-purpose models, because each advance gives defenders more capability to build on. But security is still too deep and context-dependent. That’s why we’re optimizing our entire system for security: a harness that lets models reason through code efficiently, custom models post-trained for exploitability, and full-system context that improves precision by validating exploitability.
These results are important because they mean that every defender can have access to state of the art security today, at a lower cost, and as part of a platform that is built for real security workflows. That’s why we called it the Open Defense Initiative.
Some of the largest and most impactful open source projects like FFmpeg, Envoy, Kata and many others have already signed up. If you are a defender of a critical open source project, please apply for Open Defense credits through the form at the bottom of this page.
Qasim Mithani,
Co-Founder & CEO of depthfirst
Apply now
The Open Defense Initiative is open to maintainers of widely deployed open source projects. We will prioritize software with significant downstream impact.
Before receiving access, we will ask you to prove that you are a maintainer and that your application was legitimate.
Application submitted
The depthfirst team will review your application and follow up.
-
Who is eligible for the Open Defense Initiative?
Every project must have significant downstream impact, i.e. it is deployed in critical infrastructure, embedded in widely-shipped products, or upstream of enough other software that a vulnerability would trigger coordinated disclosure at scale
-
How are projects selected?
Projects that meet the criteria will be accepted on a rolling basis based on availability.
-
How will you ensure that bad actors will not have access to depthfirst?
Before granting access, we will verify both the identity of the applicant and their authority to opt the project into the Initiative.
Identity
- The application must be tied to the project: an email on a domain tied to the project, the security contact listed in SECURITY.md, or an email matching signed commits in the repo’s recent history.
- The applicant’s GitHub/GitLab account should appear in MAINTAINERS, CODEOWNERS, or governance documents, or show a sustained record of merged commits and reviews.
- We will ask for a short public confirmation from a verifiably-theirs surface: a comment on a pinned issue, a signed message, or a note on the project’s official site or social account.
Authority
- The applicant should have merge rights or equivalent on the repo, or be explicitly delegated by someone who does.
- We will request a second maintainer to confirm the application was legitimate.
-
What happens after I submit a request?
The depthfirst team will review your application and will reach out for clarifications or to start the identity and authority verification process, if your project is accepted.
-
Where can I read about the FFmpeg vulnerabilities?
Our submissions have been accepted, but we are waiting for FFmpeg to disclose them before sharing more details. We will publish a technical blog post as soon as we are allowed.