depthfirst catches broken authorization, privilege escalation, IDOR, and subscription tier bypasses by reasoning about what your code is supposed to do
Code
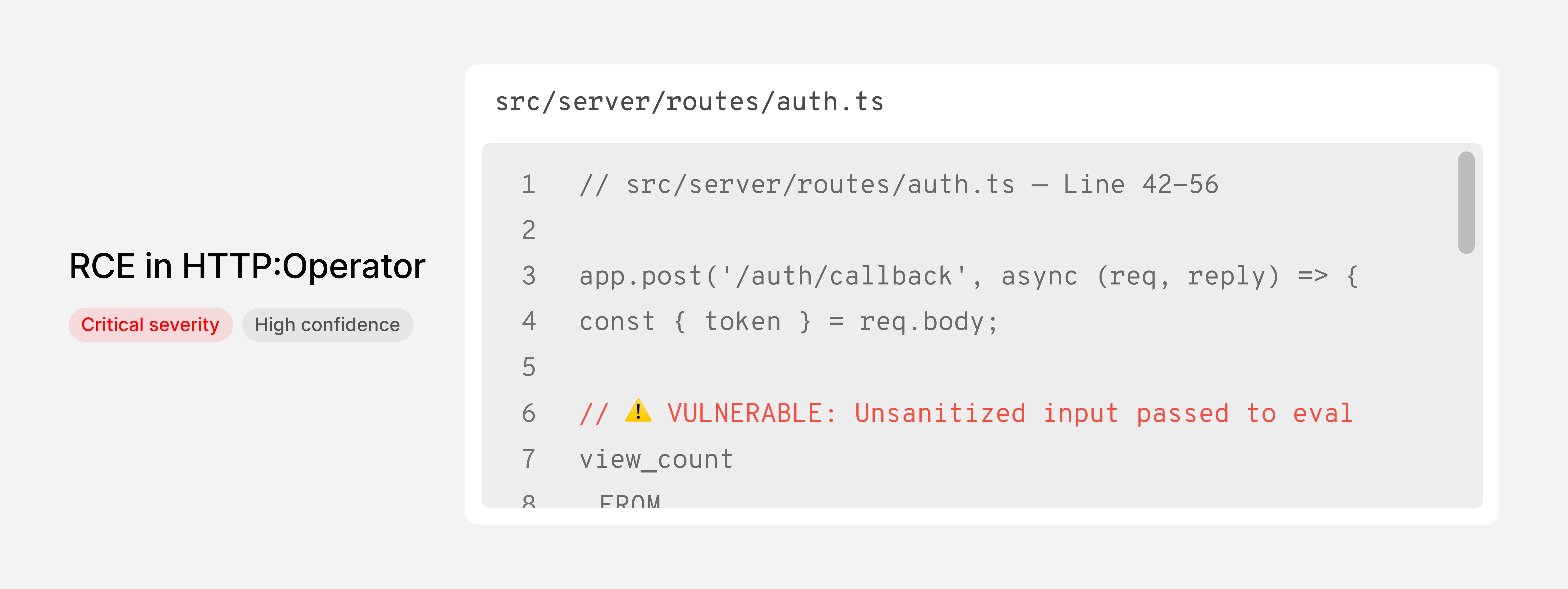
Understands your code the way a Security Engineer would. It traces business logic, mapping cross-service data flows, and surfacing real vulnerabilities it can fix autonomously.
-
-
depthfirst maps data flows across service boundaries, exposing attack paths that only exist between components—where an input in one service reaches a vulnerable sink in another.
-
depthfirst connects individual low-severity findings into exploitable paths by mapping how weak points chain together through your application’s data flows and control logic.
Find vulnerabilities hidden in your systems logic
Surface broken authorization, privilege escalation, and logic flaws by analyzing data flow, service interactions, and runtime behavior across your codebase.
![[TBD]](/uploads/Frame 2147261374.png)
Prove which vulnerabilities attackers can exploit
Eliminate false positives with full evidence trails and exploitation conditions. When conditions are met, depthfirst runs a dynamic test against your application to confirm the exploit.
![[TBD]](/uploads/Frame 2147261373.png)
Generate fixes that match your codebase
Ship fixes faster with pull request comments that match your conventions. Developers review and merge without context-switching or manual remediation.
![[TBD]](/uploads/Frame 2147261374 (1).png)
Deep scans
Analyze your entire codebase to surface the full landscape of vulnerabilities.
PR scans
Run on every pull request in 2–5 minutes, catching new vulnerabilities before merge.
Source control native
Findings surface as PR comments with one-click access to full context and generated fixes.
Developer feedback
Developers give feedback directly in GitHub to train the system and improve scanning accuracy.
Supply Chain
Trace risk through your full dependency tree and surface only the vulnerabilities with a real execution path to them.
Secrets & Sensitive Data
Detect and validate credentials across your codebase, CI/CD pipelines, and runtime environments.
Dynamic Testing
Confirm which vulnerabilities are exploitable by testing your running application with real attack paths.