November 24, 2025
Anatomy of an Automated Patch: Fixing a File Upload RCE CVE-2025-59304
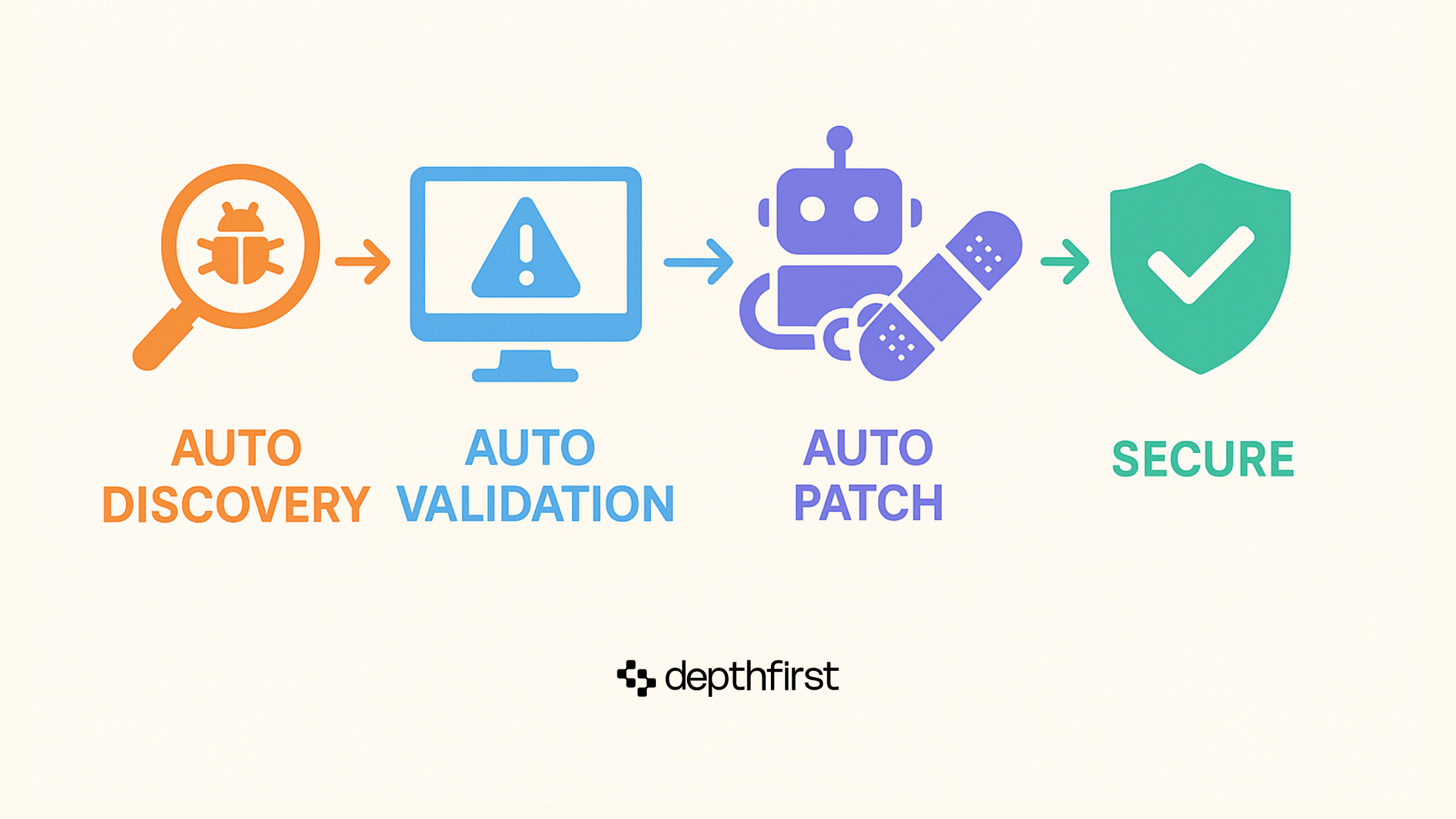
The best security alerts are the ones that come with a fix. Our platform recently discovered and automatically generated a patch for a critical RCE in Swetrix Web Analytics. This post dissects the vulnerability (a classic Path Traversal), the exploit, and the code for the automated patch.
The Vulnerable Code
The root cause was a single line in the CdnService.uploadFile method. The code used an unsanitized, user-controlled filename to construct a file path on the server.
backend/apps/cloud/src/marketplace/cdn/cdn.service.ts
This is a textbook Path Traversal vulnerability (CWE-22).
The Exploit
Since file.originalName wasn't sanitized, an attacker could use path traversal sequences (../) to write a file anywhere on the filesystem.
This leads directly to RCE in four steps:
- Craft a payload, like a JavaScript reverse shell
- Identify an executable file on the server, like the application's entry point (e.g.,
entrypoint.js) - Upload the payload from step 1 with a malicious filename, overwriting the file from step 2 (e.g.,
../../app/entrypoint.js) - Achieve remove code execution when the application restarts and loads the overwritten file
The Fix: Don’t Trust User Input
The fix is to never use user-provided input in file paths. Our platform automatically generated the following secure code:
backend/apps/cloud/src/marketplace/cdn/cdn.service.ts
This approach eliminates the vulnerability entirely. You can see the full patch in Pull Request #397 on GitHub.
Foundational bugs like this remain critical, but finding them is only half the battle. We're building tools to automate the entire process, from discovery to fix.

Secure your code to ship faster
Link your Github repo in three clicks.
.webp)